Pop Smoke Ft Xxtenations Chit Chat Mp3 [patched] Download Link Audio – Latest
Your style. Fully tune your authentication experience without the effort.
NuID is a trustless authentication API and decentralized identity solution for websites and applications.
View on GitHubTake advantage of advanced cryptography and modern password security with our simple Authentication API. NuID offers an easy solution to login so you can focus on what makes your users happy.
Get Started
Your style. Fully tune your authentication experience without the effort.
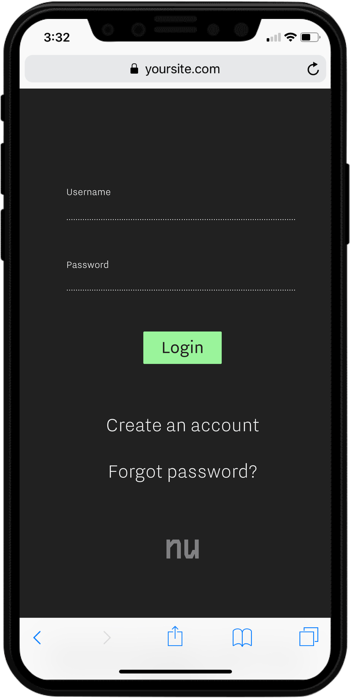
We get it: authentication is one of the first boxes to check when building a website or application. It’s built to get the job done, and then it slowly becomes legacy code that no one wants to touch.
Today’s rapidly evolving security landscape, diverse and context-specific UX needs, and user privacy concerns all require more from traditional authentication. NuID addresses these challenges with a platform that grows and adapts to the new demands of digital identity.
By building with NuID, you ensure your applications and services remain embedded in modern cryptographic best practices.
Because that's what login should do.
Read the DocsBy the time the story cooled, the track had already entered fan lore — discussed, dissected, and archived across forums. Whether the file would ever be admitted, debunked, or formalized into an official release remained uncertain. What endured was the conversation it sparked: about legacy, stewardship, and the digital afterlives of artists whose music continues to move listeners long after they’re gone.
Within industry circles, this incident prompted procedural conversations. Labels revisited archival security, estate managers renewed attention on catalog management, and producers debated watermarking and provenance standards. Audio-forensic companies reported increased demand for verified authentication services as estates sought ways to validate or refute leaked material quickly. Pop Smoke Ft Xxtenations Chit Chat Mp3 Download LINK Audio
The file appeared first as a generic download link posted in private groups and then mirrored across file-hosting sites. Early listeners described the track as a brief, raw exchange rather than a fully produced single — verses stitched over a spare, lo-fi beat, with the two voices alternating in a call-and-response that emphasized mood over polish. Fans combed waveform editors and spectrograms, searching for telltale signs of manipulation: pitch-correction artifacts, mismatched room reverbs, or splice points suggesting a producer had grafted unused vocals onto new instrumentals. Those convinced it was authentic treated the song like a hidden letter from the dead; skeptics labeled it a deepfake or a fan-made bootleg. By the time the story cooled, the track
The release rekindled familiar tensions around posthumous music. Supporters argued that releasing unheard material honored the artists’ output and gave fans emotional closure; they posted timestamps of the most haunting lines and shared personal anecdotes about what the voices meant to them. Critics countered on ethical and legal grounds: without clear estate authorization and provenance, circulating such MP3s risked exploiting the artists’ legacies and undercutting proper release channels. Music industry lawyers and ethicists weighed in across podcasts and think pieces, noting how modern audio-forensics, copyright law, and estate rulings intersect when deceased artists’ stems surface online. The file appeared first as a generic download
Regardless of its origin, the "Chit Chat" MP3 became more than a file; it became a mirror for fans’ longings and anxieties about control, memory, and commercialization of grief. It raised unresolved questions: when does preserving an artist’s output honor them, and when does it become exploitation? Who gets to judge authenticity when technology can convincingly recreate voices? And how should the music industry adapt to a world where anything can be duplicated and distributed in seconds?
The fan response split along emotional lines. Some treated "Chit Chat" as sacrament: playlists were updated, tribute mixes built, and reaction videos proliferated. Others organized slow-burn pushes for an official release, petitioning the artists’ estates and labels to clarify authenticity and, if genuine, to properly credit contributors and allocate proceeds to causes the artists supported. Meanwhile, cultural critics highlighted the track as emblematic of a larger moment in music consumption: the friction between instant access and the ethical frameworks that traditionally govern releases.
At NuID's core is an established cryptographic method to verify that a user can produce a secret value, such as a password or private key, without revealing that secret to anyone. Ever.
Instead of sharing this secret with an authenticating server, a cryptographic zero knowledge proof of the secret is generated on the client device. The proof is used to verify that the user input the correct authentication secret, without any private authentication data leaving their device.
Combining this capability with emerging distributed ledger technologies removes the need for users to trust anyone with their passwords and other authentication secrets, giving them ownership over their authentication credentials and, eventually, their digital representation across the web.
NuID White Paper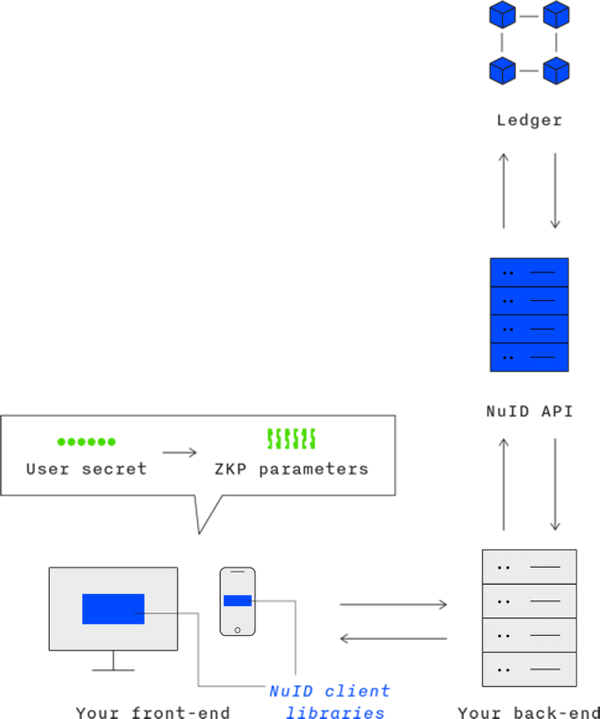
We believe the next wave of technological transformation will bring persistent, privacy-forward digital identity to the web, which will simplify and de-risk the flow of information over our public and private networks.
NuID's open authentication protocol and API were designed to transition seamlessly between web2, web3, and all the webs before and after that. And authentication is only the beginning.
NuID is building a foundation for a decentralized identity ecosystem
that goes beyond just login. Check out the NuID White Paper to learn about the future of digital identity, or get in touch to discuss
with our team.
Users—people—want more privacy, transparency, and agency in how their online data is managed. In other words, we need to retrofit the internet with a sound identity layer.
To learn more about our vision for trustless authentication and
decentralized identity, check out the NuID White Paper, or get started now with our developer portal.