






The from the Laura's Candy Doll Collection is a noteworthy collectible item. Its value and appeal are derived from its design, condition, and the niche market it occupies. For collectors and enthusiasts, keeping abreast of market trends and the specific details of this doll can be crucial for both acquisition and valuation purposes.
The Laura's Candy Doll Collection is a series of collectible dolls created by a renowned manufacturer. This report focuses on a specific item within the collection: . The objective is to provide a comprehensive overview of this particular doll, highlighting its features, condition, and overall significance within the collection.
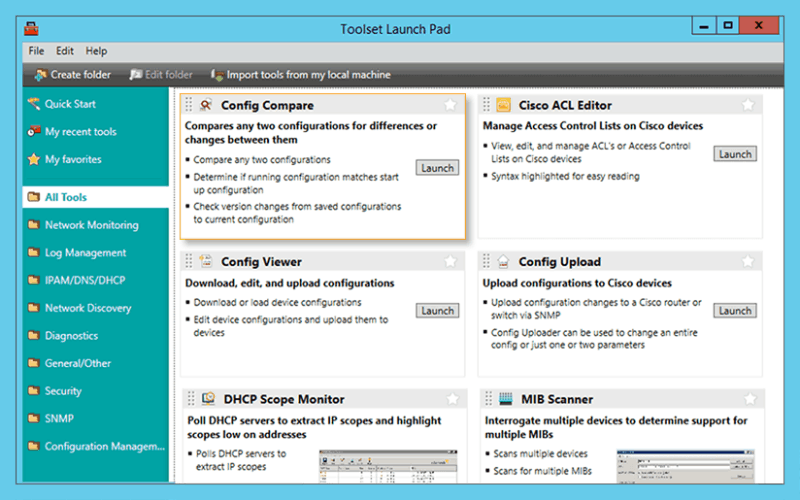
Troubleshoot network issues that arise due to configuration changes.
Download a configuration file from a Cisco CMTS or network router to a PC.
Upload configuration changes to a Cisco router or switch via SNMP.
Access essential network and device configuration management tools to help you stay on top of config changes.
Easy-to-use tool for remotely and quickly configuring NetFlow v5 via SNMP on supported Cisco devices.
The from the Laura's Candy Doll Collection is a noteworthy collectible item. Its value and appeal are derived from its design, condition, and the niche market it occupies. For collectors and enthusiasts, keeping abreast of market trends and the specific details of this doll can be crucial for both acquisition and valuation purposes.
The Laura's Candy Doll Collection is a series of collectible dolls created by a renowned manufacturer. This report focuses on a specific item within the collection: . The objective is to provide a comprehensive overview of this particular doll, highlighting its features, condition, and overall significance within the collection.
Significantly reduce the time required to isolate and identify a bandwidth or network segment failure.
Generate a "Magic Packet" to remotely power on PCs attached to networks.
Protect your enterprise network with a strong password generator.
Decrypt any Cisco type-7 passwords for routers and switches. laurab candy doll collection 8 b cdcl 008 307 best
Attack an IP address with SNMP queries to determine the SNMP read-only and read-write community strings.
Use permuted hacker dictionaries to attack devices in an attempt to break into them or discover community strings.
Perform Domain Name System-based Blackhole List (DNSBL) checks. The from the Laura's Candy Doll Collection is
Remotely discover the devices that are connected to each port on a switch or hub.
Perform network stress tests with WAN Killer.