SCREENSHOTS
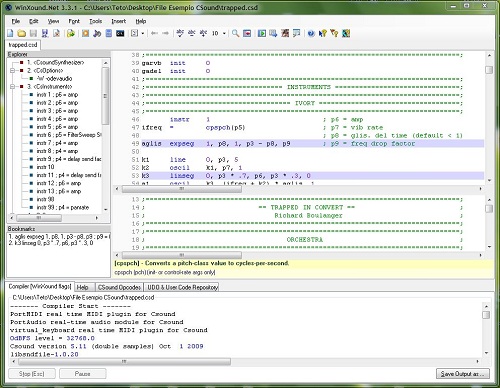
WinXound for Windows
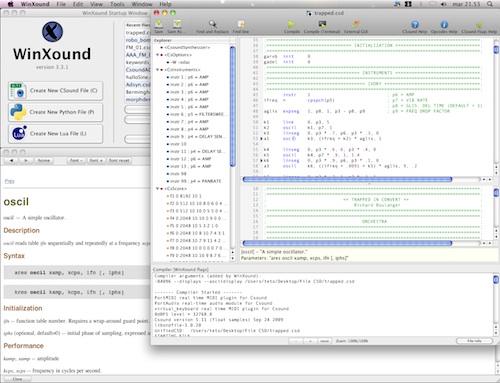
WinXound for OsX
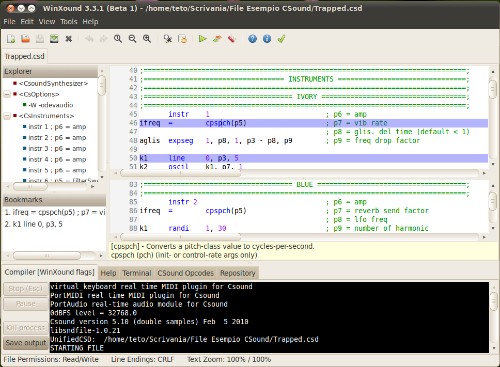
WinXound for Linux
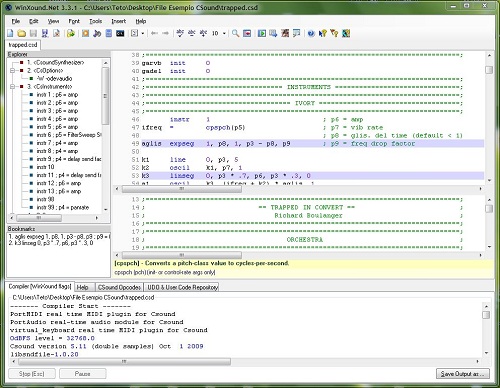
WinXound for Windows
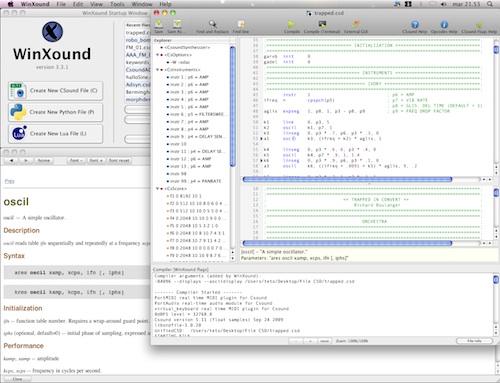
WinXound for OsX
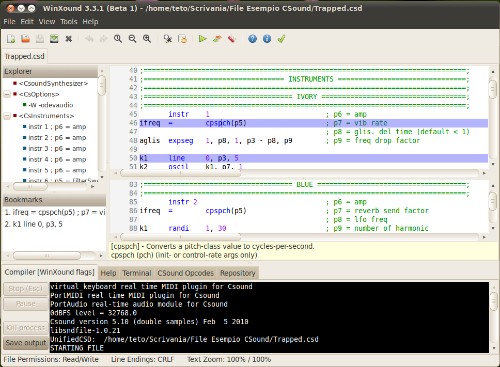
WinXound for Linux